Face Recognition Access Control Software


Access Control Software Pricing
- Essential
Ideal for small businesses, requires an internet connection and an Android device. Includes liveness verification to confirm user identity.
$0.8/mo
Per employee + $19.0 /mo Base Rate- Check-in Options:
– Android App - Attendance Dashboard
- 24/7 Tech Support
- Check-in Options:
- Business
Suitable for medium to large businesses, operates offline. Advanced liveness verification through video and is compatible with cameras.
$1.0/mo
Per employee + $99.0 /mo Base Rate- Check-in Options:
– Android App
– Web-camera - Attendance Dashboard
- 24/7 Tech Support
- Offline Recognition
- Advanced Liveness Detection
(certified by iBeta)
- Check-in Options:
- Ultimate
Customized for the needs of large organizations, offers comprehensive solutions for time tracking and access control.
Contact Us- Check-in Options:
– Android App
– Web / CCTV-camera - Attendance Dashboard
- Personal Manager
- Offline Recognition
- Advanced Liveness Detection
(certified by iBeta)
- Check-in Options:
Ultimate Plan
It supports various Check-in/out Options including Android Device, Web-camera, IPTV-camera, and Web App integration.
Tailored for environments with over 1,000+ visitors or employees, this plan also includes a dedicated manager to ensure optimal operation.

Use Cases



How It Works





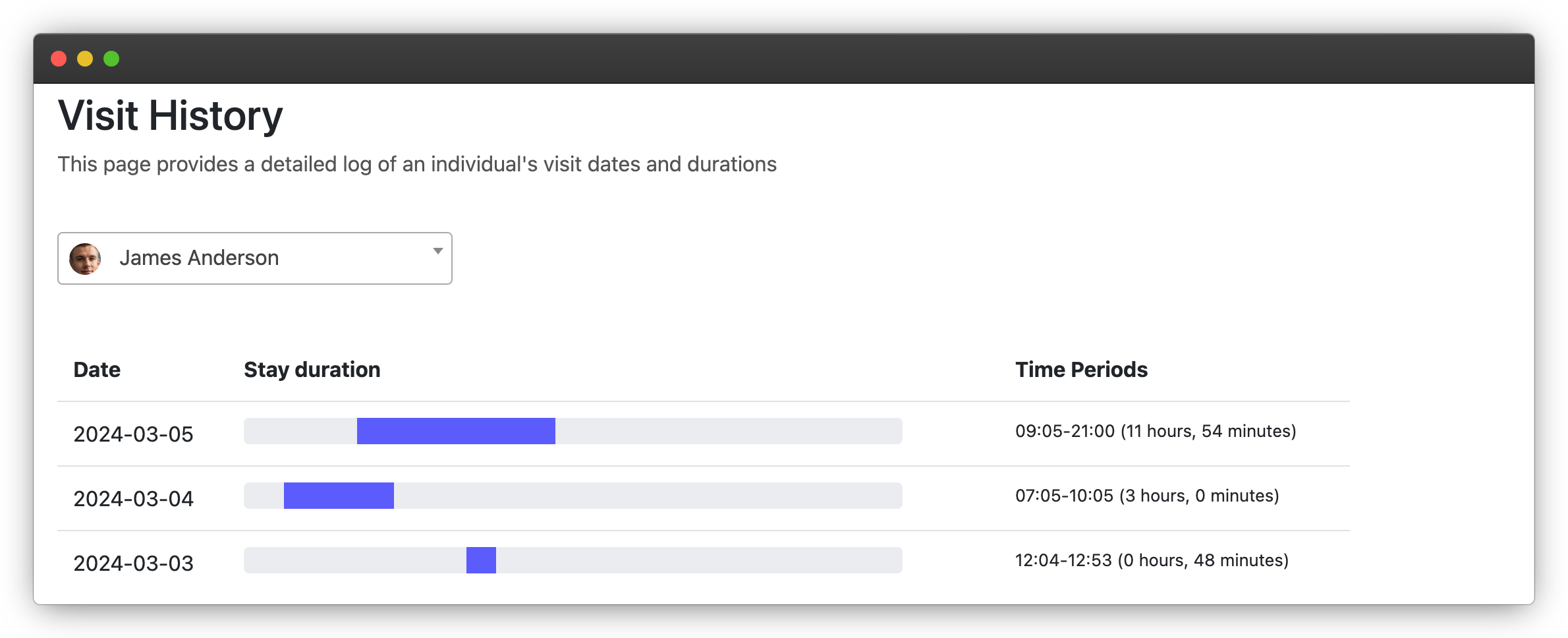
Tracking Specific Visitor Dates
Our first dashboard provides dates and times when an individual entered a building or room, useful for employee time tracking or student attendance records. For gyms, this data can help understand customer frequency and manage peak times.
 Get Free API Requests
Get Free API Requests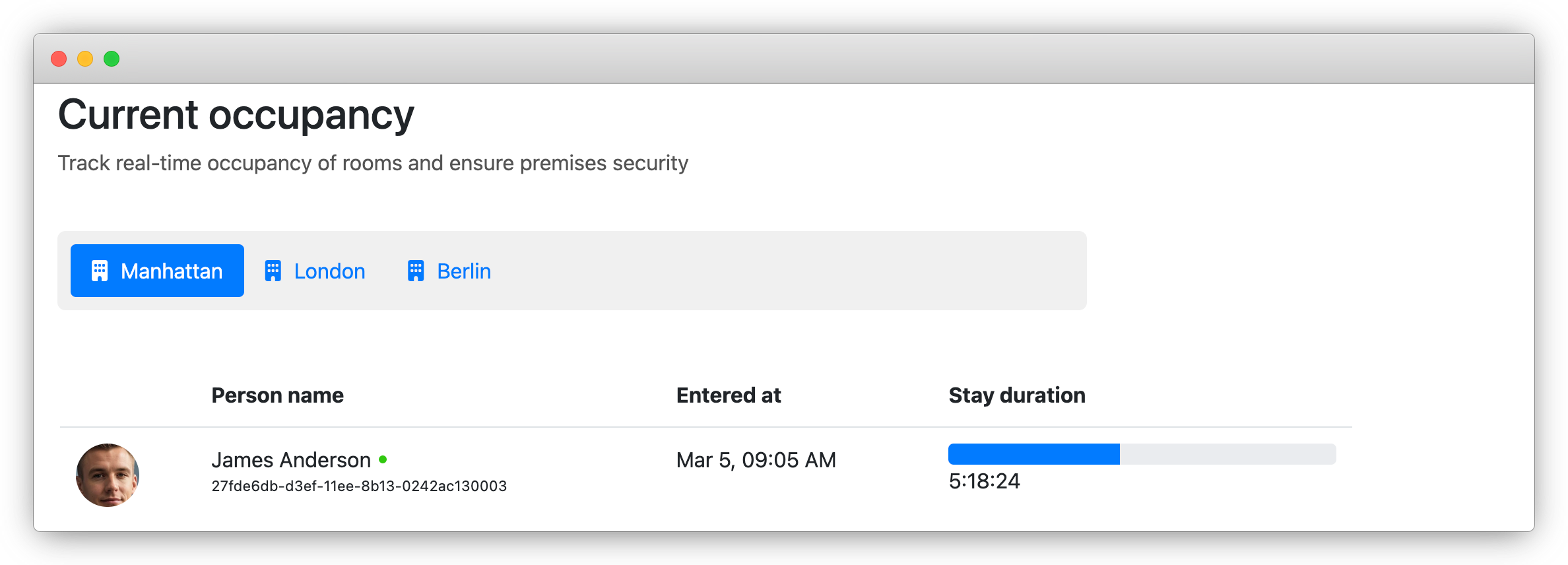 Get Free API Requests
Get Free API RequestsMonitoring Current Occupancy
To keep track of who is currently in your buildings or rooms, our "Current occupancy" feature provides real-time information about everyone who has checked in.
Viewing Daily Attendance
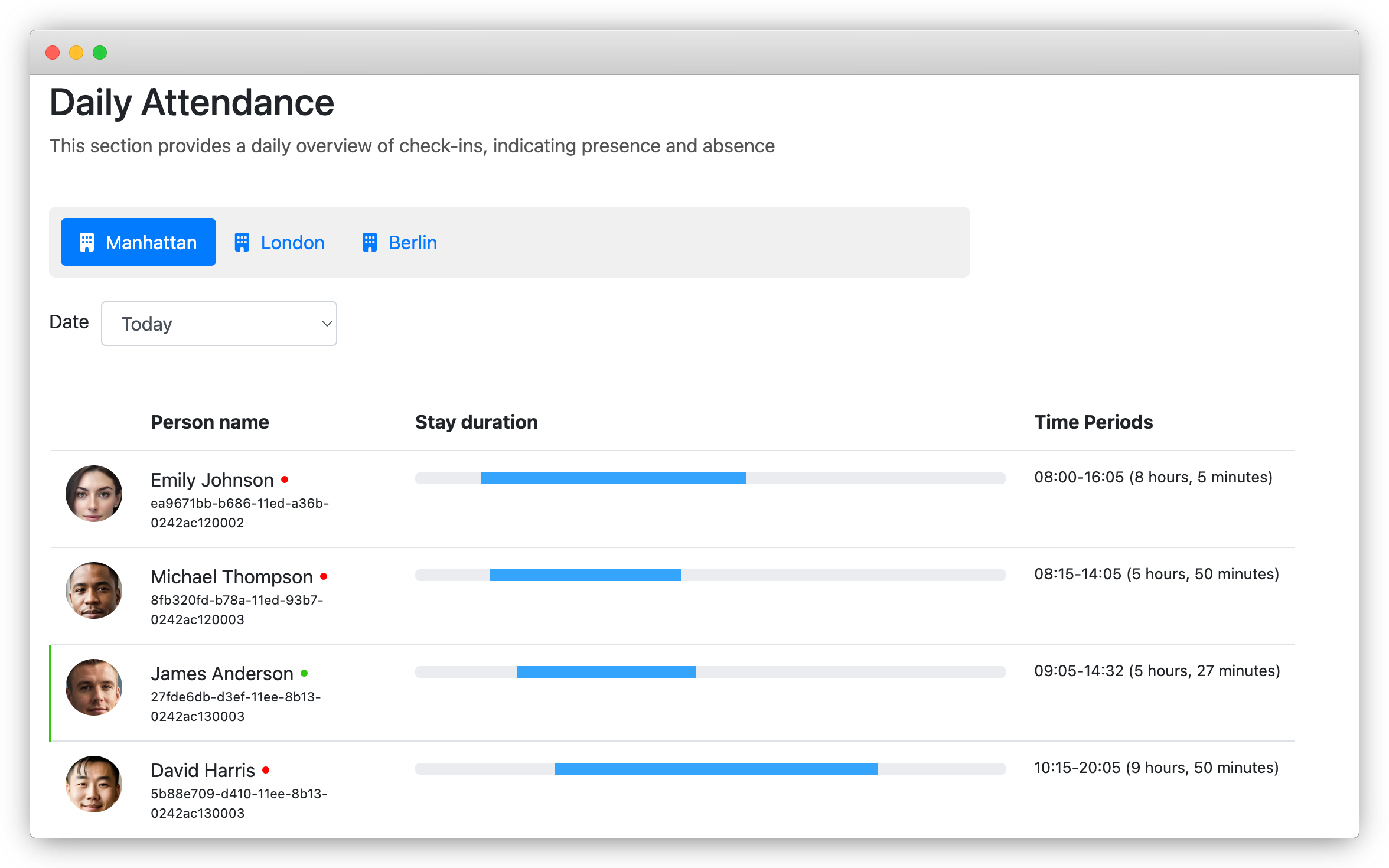
With the "Daily attendance" feature, you can see who was in the facility on any given day, their arrival and departure times, and identify those who are still present, highlighted in green.
Get Free API Requests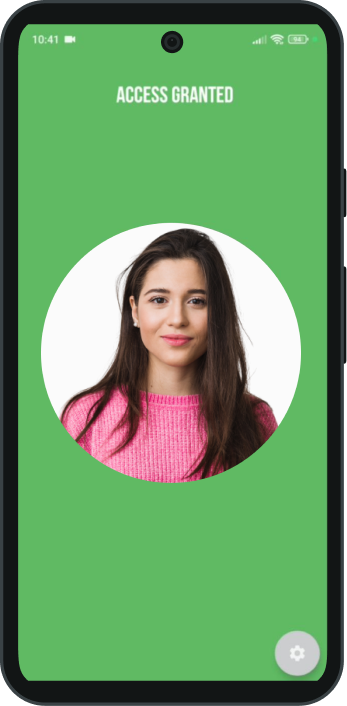 Get Free API Requests
Get Free API RequestsAndroid Face Recognition Access Control App
The Luxand.cloud facial recognition check-in/out app provides instant feedback with color coded responses. As a visitor approaches and looks into the device, the facial recognition process begins. The screen turns blue while the image is processed. A green screen means welcome, while red indicates a blacklisted visitor triggering an alarm. If recognition fails, the screen turns orange, indicating the visitor should adjust their position and try again.
Access Control Software Benefits
The average cost of a data breach in the US is a staggering $4.24 million, according to IBM Security. Facial recognition can significantly reduce the risk of unauthorized access.
A study published in the Journal of Security and Privacy reported a 50% decrease in unauthorized access attempts and security breaches after implementing facial recognition in commercial buildings.
According to the Ponemon Institute study, 90% of employees prefer facial recognition access for its convenience and ease of use.